Perceptions | 0xFun CTF 2026
a writeup for "Shell" in 0xFun CTF 2026.
Overview
- Platform: 0xFun
- Challenge: Perceptions
- Categories: Web
- Rating: 9/10
- Difficulty: Easy
- Sovling Time: ~20 Minutes
Challenge
“Take a look at the blog I created! It has a neat backend and, interestingly, seems to use fewer ports.”
Walkthrough
Recon
The website looks very normal, just we have a login page, later on that later.
Something looks fishy in Secret Post, by viewing the page source we can see some credentials: 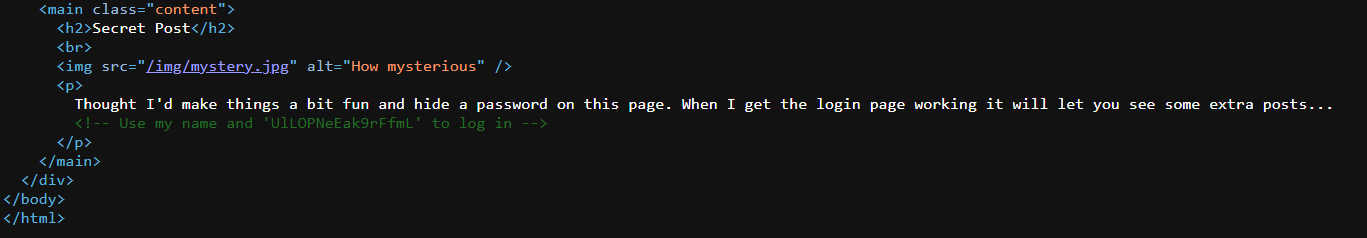
Solution Approach
“Flag format:
0xfun{}”
From recon we can try credentials we found in the login page
Username is
Charlie, you can see this at top of the site.
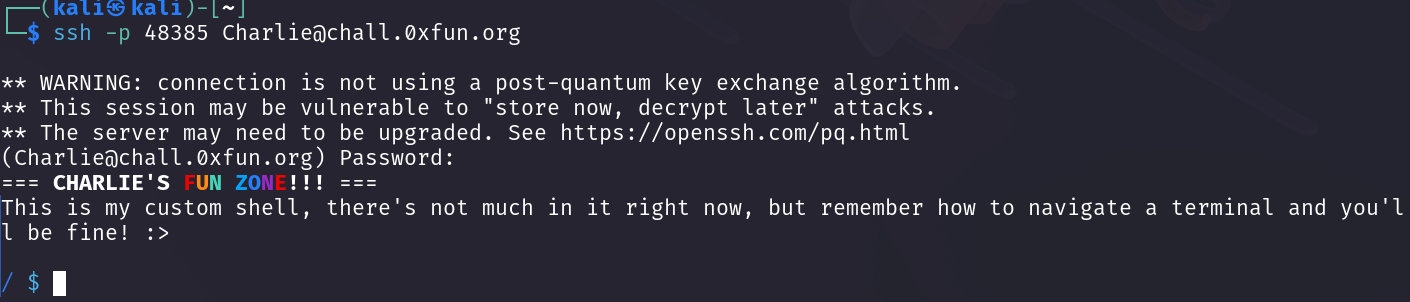
Nothing has changes….. Wait they mentioned in a blog something about many things running on many ports, lets try to SSH into the server with the provided credentials.
1
ssh -p 48385 Charlie@chall.0xfun.org
And it worked!! Lets find the flag.
Flag
0xfun{p3rsp3c71v3.15.k3y}
Hope you enjoined the writeup, Don’t forget to leave a comment or a star on the github repo (;