DigDug | TryHackMe
Here we will explore how to solve "DigDug" challenge on TryHackMe
Overview
- Platform: Tryhackme
- Challenge: DigDug
- Categories: Misc, Machines
- Rating: 8/10
- Difficulty: Very Easy
- Solving Time: ~3 minutes
Challenge
“Oooh, turns out, this MACHINE_IP machine is also a DNS server! If we could dig into it, I am sure we could find some interesting records! But… it seems weird, this only responds to a special type of request for a givemetheflag.com domain?”
Walkthrough
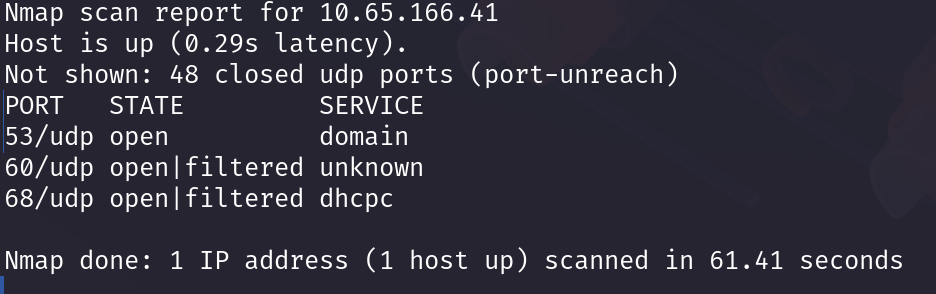
Recon
Always start with nmap scan, since we’re looking for UDP based service we should use -sU flag. so final command is:
1
nmap -sC -sU -p 50-100 MACHINE_IP
I only used
-pflag in nmap to reduce the scanning time, otherwise you can scan normally.
Solution Approach
“Retrieve the flag from the DNS server!”
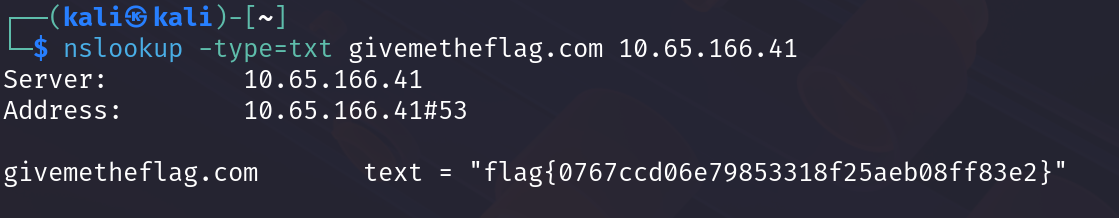
Hmm looks we have DNS server at port 53 lets use nslookup to check its TXT records!
1
nslookup -type=txt givemetheflag.com MACHINE_IP
and Tatadaa!
Flag
flag{0767ccd06e79853318f25aeb08ff83e2}
Hope you enjoyed the writeup, Don’t forget to leave a comment or a star on the github repo (;